Google Workspace là bộ ứng dụng văn phòng chuyên nghiệp gồm các ứng dụng năng suất cộng tác. Dễ dàng làm việc trên email, lịch, tài liệu, bảng tính và trang trình bày trên các thiết bị của bạn, có hoặc không có internet. Giữ tất cả công việc của bạn ở một nơi với quyền truy cập an toàn từ máy tính, điện thoại hoặc máy tính bảng của bạn.
Tính năng
- Calendar
- Instant Messaging
- Video Conferencing
- Documents
- Spreadsheets
- Slides
- Drive
- Note taking
- Forms
Lợi ích
- Ra quyết định nhanh hơn, mặt đối mặt
- Cộng tác trong thời gian thực
- Lưu trữ và chia sẻ tệp trên đám mây
- Bảo mật dữ liệu và thiết bị của bạn
- Dễ dàng kết nối, tạo, truy cập và kiểm soát
- Starter Edition bao gồm 30GB dung lượng lưu trữ
- Bạn nhận được hỗ trợ trực tiếp 24/7
- Dễ dàng di chuyển dữ liệu của bạn sang Google Workspace
- Mọi thay đổi được lưu tự động
Service scope
System requirements
- A modern web browser
- Please refer to https://gsuite.google.com for more information on technical requirements
User support
P1 within one hour (24 x 7) and P2, P3, and P4 within 1 business day.Premium Support is available at an additional cost, which includes a 15 minute intial response target.Priorities defined: https://support.google.com/a/answer/1047213
Technical Support Services Guidelines: https://gsuite.google.com/terms/tssg.html
*NOTE: Response times may vary for G Suite for Education customers
**NOTE: Phone support is not available with the free edition of G Suite or Cloud Identity.
***New Support packages will be launched in Q4 2020 / Q1 2021. Follow updates: https://cloud.google.com/support
Support levelsG Suite customers are eligible for Basic/Free support at no additional cost. Premium Support is available at an additional cost. Premium Support includes improved target response times and Technical Account Manager support services.
Support services are described in more detail here: https://gsuite.google.com/terms/tssg.html.
**New Support packages will be launched in Q4 2020 / Q1 2021. Check here for updates: https://cloud.google.com/support
Onboarding and offboarding
We also povide G suite training which is a plug-in to your Chrome and describes step-by step functionalities and processes.
The G suite Learning Center https://gsuite.google.com/learning-center/ provides numerous documentation, guides, tips, customer examples, and training resources”
Documentation formats
- HTML
- Other
https://support.google.com/a/answer/1257646#direct_step2_cancel_subscriptions”
Using the service
Supported browsers
- Internet Explorer 7
- Internet Explorer 8
- Internet Explorer 9
- Internet Explorer 10
- Internet Explorer 11
- Microsoft Edge
- Firefox
- Chrome
- Safari 9+
- Opera
Compatible operating systems
- Android
- IOS
- MacOS
- Windows
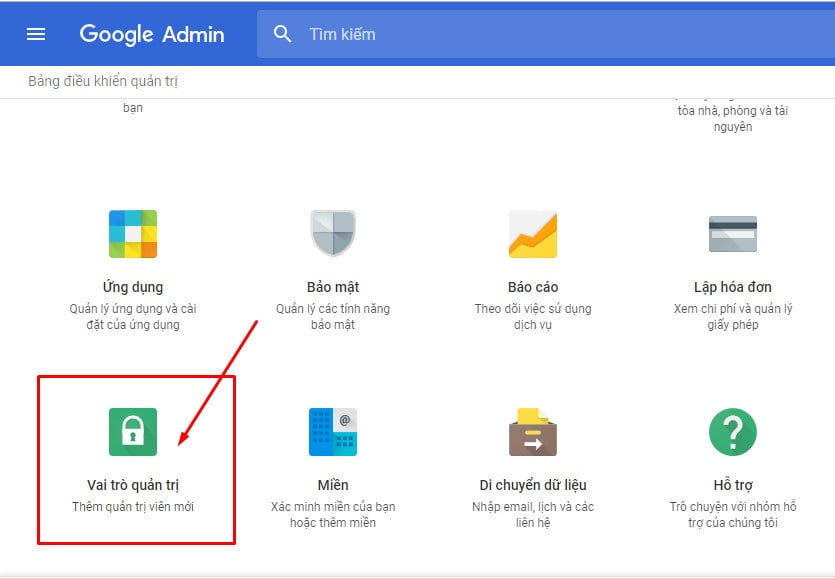
Easily add users, manage devices, configure security and settings so your data stays safe.
Use integrated Cloud Identity features to manage users and set up security options. Protect your organization with security analytics and best practice recommendations within the security center.
Distribute apps to employees and keep data secure on employee’s iOS and Android devices. Use mobile management to distribute apps and get employees up and running quickly, check usage, manage security settings, and lock or wipe devices remotely.
Limit the geographical location of your covered G Suite data at rest.
API documentation formats
- HTML
With Apps Script, you can create Add-ons for Google Docs, Macros, menus, and custom functions as well as managing responses for Google Forms”
Scaling
Analytics
– Security: Assess overall exposure to data breach. Discover which users not using 2-step verification, installing external apps, or sharing documents indiscriminately.
– Apps Usage Activity: See how your organization uses G Suite over a specific period by examining email activity, number of spreadsheets created, number of files shared, and more.
– Account Activity: Access all data from Security, Apps Usage Activity, and Highlights pages in a single master report.
– Audits: View logs of various activity, including admin, mobile activity, and more.
More: https://support.google.com/a/topic/29163?hl=en&ref_topic=4490889″
Reporting types
- API access
- Real-time dashboards
- Regular reports
- Reports on request
Resellers
Staff security
Asset protection
Data storage and processing locations
- United Kingdom
- European Economic Area (EEA)
- EU-US Privacy Shield agreement locations
Protecting data at rest
- Physical access control, complying with CSA CCM v3.0
- Physical access control, complying with SSAE-16 / ISAE 3402
- Encryption of all physical media
- Scale, obfuscating techniques, or data storage sharding
- Other
Other data at rest protection approach”Data belonging to G Suite customers is stored at rest in two types of systems: disks and backup media.
Disks are used to write and retrieve data in multiple replicated copies. (For more information on this replication of data, please see the G Suite Security Whitepaper.) Google also stores data on offline backup media to help ensure recovery from any catastrophic error or natural disaster at one of our data centers.
Data stored at rest is encrypted on both disks and backup media, but for each system we use a distinct approach for encryption to mitigate the corresponding security risks.”
Data importing and exporting
https://support.google.com/accounts/answer/3024190?hl=en”
Data export formats
- CSV
- ODF
- Other
Other data export formats
- DOCX
- XLSX
- PPTX
Data import formats
- CSV
- ODF
- Other
Other data import formats
- DOCX
- XLSX
- PPTX
Data-in-transit protection
Availability and resilience
https://www.google.com/appsstatus#hl=en-GB&v=status
Identity and authentication
User authentication
- 2-factor authentication
- Public key authentication (including by TLS client certificate)
- Identity federation with existing provider (for example Google Apps)
- Dedicated link (for example VPN)
- Username or password
- Other
creation and to the System Administrators of the tenant whom can decide to force a password change on any user that is later detected to have a password that is weak. Google’s native authentication has
protections in place that would detect a brute force attack and challenge the user to solve a Captcha and would auto lock the account if suspicious activity is detected. The tenant’s System Administrators can
reset that account for the end user.”
Access restrictions in management interfaces and support channels”G Suite provides administrative features made available to Customer within the Admin Console for the management of Google-hosted accounts, mobile devices, and application within the Customer’s domain. Advanced security and control features may be subject to an additional charge
Support services are only provided to authorized customer administrators whose identities have been verified in several ways. Googler access is monitored and audited by our dedicated security, privacy, and internal audit teams.
https://cloud.google.com/iam/
https://cloud.google.com/security/overview/whitepaper#administrative_access
https://cloud.google.com/files/Google-Cloud-CSA-CAIQ-January2017-CSA-CAIQ-v3.0.1.pdf”
Management access authentication
- 2-factor authentication
- Public key authentication (including by TLS client certificate)
- Identity federation with existing provider (for example Google Apps)
- Dedicated link (for example VPN)
- Username or password
- Other
maximum or increase the minimum. A Password Monitor is visible to the end user upon password
creation and to the System Administrators of the tenant. Google’s native authentication has
protections in place that would detect a brute force attack and challenge the user if suspicious activity is detected. System Administrators can reset that account for the end user.
Google provides the capability for domain administrators to enforce Google’s 2-step verification. The 2nd
factor could be a code generated via several supported mechanisms.
Audit information for users
Standards and certifications
Security governance
Security governance standards
- CSA CCM version 3.0
- ISO/IEC 27001
https://cloud.google.com/security/overview/whitepaper
https://cloud.google.com/security/compliance”
Operational security
Vulnerability management approach”Google administrates a vulnerability management process that actively scans for security threats using a combination of commercially available and purpose-built in-house tools, intensive-automated and manual penetration efforts, quality assurance processes, software security reviews and external audits. The vulnerability management team is responsible for tracking and following up on vulnerabilities. Once a vulnerability requiring remediation has been identified, it is logged, prioritized according to severity, and assigned an owner. The vulnerability management team tracks and follows up frequently until remediated. Google also maintains relationships with members of the security research community to track issues in Google services and open-source tools.
https://cloud.google.com/security/overview/whitepaper#vulnerability_management”
Protective monitoring approach”At many points across our global network, internal traffic is inspected for suspicious behavior, such as the presence of traffic that might indicate botnet connections. This analysis is performed using a combination of open-source and commercial tools for traffic capture and parsing. A proprietary correlation system built on top of Google technology also supports this analysis. Network analysis is supplemented by examining system logs to identify unusual behavior, such as attempted access of customer data. Google security engineers place standing search alerts on public data repositories to look for security incidents that might affect the company’s infrastructure.
https://cloud.google.com/security/overview/whitepaper#monitoring”
Incident management approach”We have a rigorous incident management process for security events that may affect the confidentiality, integrity, or availability of systems or data. This process specifies courses of action, procedures for notification, escalation, mitigation, and documentation. Google’s security incident management program is structured around the NIST guidance on handling incidents (NIST SP 800–61). Key staff are trained in forensics and handling evidence in preparation for an event, including the use of third-party and proprietary tools. Testing of incident response plans is performed for key areas, such as systems that store sensitive customer information.
https://cloud.google.com/security/overview/whitepaper#incident_management”